IOT Security
It’s a physical object that connects to the Internet. It can be a fitness tracker, a thermostat, a lock or appliance – even a light bulb.
Imagine shoes that track your heartbeat… and can flag potential health problems. You don’t have to imagine – these “smart” shoes already exist!
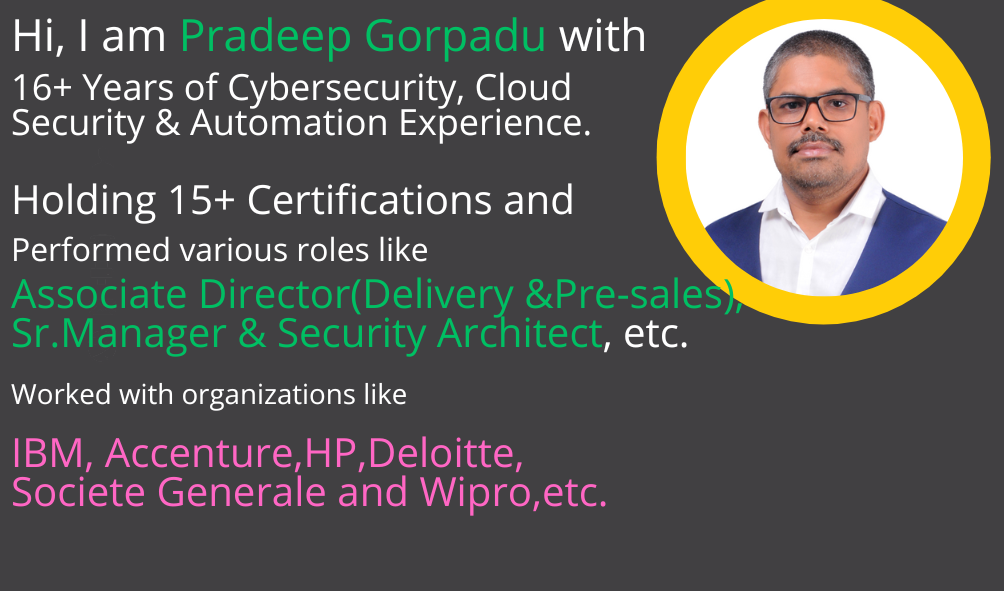
About Mentor
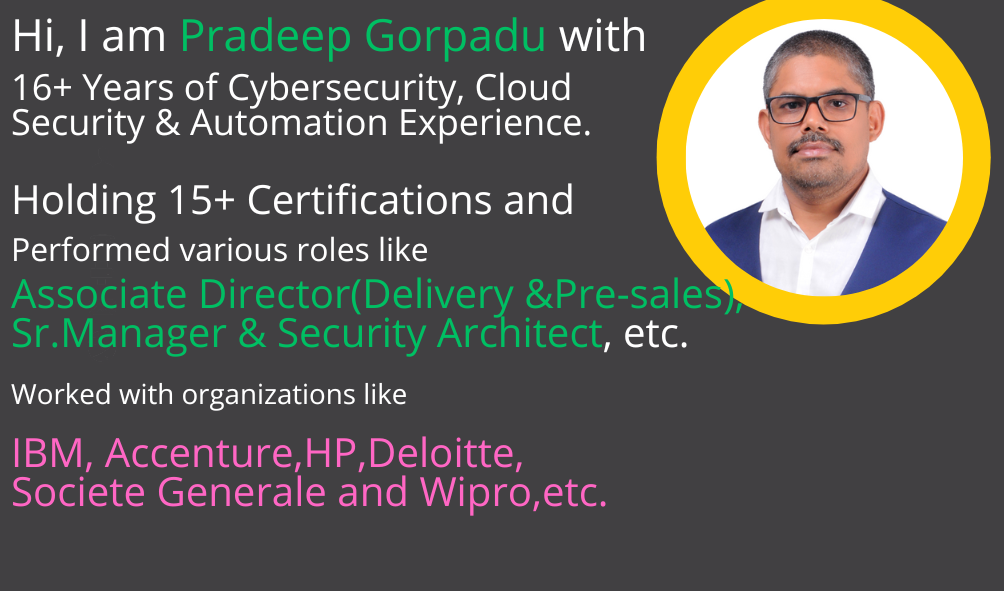
COMPLETED THE BELOW LIST OF MOST VALUABLE CERTIFICATIONS IN IT SECTOR, INCLUDING:
- CISM (Certified Information Security Manager)
- Microsoft Cybersecurity Architect (SC100)
- Microsoft Security Operations Analyst (SC200)
- Microsoft Azure Security Technologies (AZ500)
- Microsoft 365 Security Administration (MS500)
- Microsoft Identity and Access Administrator
- Professional Scrum Master
- Professional Cloud (Google Cloud) Security Engineer
- ChatGPT-AI in Cybersecurity
- ITIL V3 in IT Service Managemen
- Azure Architect Technologies (AZ300)
- Microsoft Information Protection (SC400)
- Prince2 Practitioner
- SAFe4 Agilist
What is IoT security (internet of things security)?
IoT security (internet of things security) is the technology segment focused on safeguarding connected devices and networks in IoT. IoT involves adding internet connectivity to a system of interrelated computing devices, mechanical and digital machines, objects, animals and people. Each thing has a unique identifier and the ability to automatically transfer data over a network. However, enabling devices to connect to the internet opens them up to serious vulnerabilities if they aren’t properly protected.
The term IoT is extremely broad, and as this technology continues to evolve, the term only becomes broader. From watches to thermostats to video game consoles, nearly every technological device can interact with the internet, or other devices, in some capacity.
IoT security is even broader than IoT, resulting in a variety of methodologies falling under that umbrella. Application programming interface (API) security, public key infrastructure (PKI) authentication and network security are just a few of the methods IT can use to combat the growing threat of cybercrime and cyberterrorism rooted in vulnerable IoT devices.
Why is IoT security important?
Due to the unconventional manufacturing of IoT devices and the vast amount of data they handle, there’s a constant threat of cyber attacks. Several high-profile incidents where a common IoT device was used to infiltrate and attack the larger network have drawn attention to the need for IoT security.
you will learn:
- How you can get started with IoT pentesting right now. Are you confused by reading so many different blogs and articles and don’t know where to begin? This training series on IoT Security by Attify will help you kickstart your journey and point you in the right direction.
- How to look at firmware including a hands-on example. What to do when you have a firmware binary? How do you possibly assess it for security issues? An actionable to-the-point email.
- Ways to identify and exploit vulnerabilities. Even though it’s a very short training, I’ll try to highlight some of the ways in which you can identify and exploit vulnerabilities in Smart IoT devices.
- Embedded Device Hacking. Never touched hardware before? Don’t worry. I will mention about ways to get started with hardware hacking and how you can get started playing with hardware to find vulnerabilities in IoT devices.
- Software Defined Radio for Hackers. What is SDR and what is it used for? How you can get started working with radio signals and take the advantage of the enormous power SDRs possess (including tools you can use to get started).
- Bluetooth Low Energy Exploitation. I have hacked tons of devices by attacking BLE and other communication protocols. I’ll share some of the ways in which you can exploit BLE and how to take that knowledge to other protocols.